Home » Ch 2 – basic terminology and concepts (Page 2)
Category Archives: Ch 2 – basic terminology and concepts
Wifi security
image from tinker-tailor-solider-spy.com
While networks have many advantages – the key one being connected systems and data – their key problem is security. The only way to be absolutely certain that data transmitted on a network is secure is secure is to encrypt it – and this is an issue of much debate in recent times.
While a wired network may offer some physical security – hackers have to get one the premises effectively – wireless networks have always had an issue in that they can be “scanned”. Many of use have probably used unsecure/free public wifi on a bus or in a coffee shop. This is fine once you are not sending confidential information.
And I am sure many of us have used the sometimes costly wifi in hotels. We may think as we pay, it is more secure. A recent blog post on the Economist suggests otherwise. The post notes a report by Kaspersky Labs, which found that specific persons staying in hotels were targeted and their hotel wifi connection snooped. This was down to some clever malicious software, but the lesson to be learned for a business might be – assume all wifi you do not control is unsecure.
Technology number 2 concern of Boards
A recent report cited on CGMA’s website places technological risk at the second risk concern amongst a survey of Boards of Directors. The risk concern is with cyber-security, and was the number one risk concern of private firms. The report notes an increases in the perceived technology risk from previous years. It is interesting (and good) that Boards are well aware of technological risk – as most large organisations today are so reliant on their information systems. You can read the full report here and the CGMA article here.
The cloud – Dropbox
Here is a nice new feature from BBC on cloud storage company DropBox
Technological progress 2
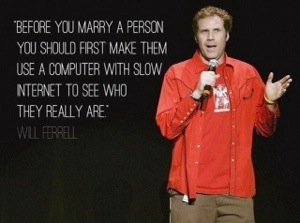
Following from our last post, have a look at this:
I came across it on a social network. If you are a student, you may be too young to remember when Internet speeds were 64Kb per second or so – yes that’s Kb not Mb per second. Nowadays 40-50 Mb is normal at home and in business. That’s nearly 1000 times faster.